The hacking term “phishing” has become so common that it is rare today to come across a person who has never heard of it. That said, often there is still a lot of confusion about what it really is and just how easy it is to fall victim. In fact, while more people might be familiar with the term, the amount of people actually falling victim to phishing attacks has increased. According to a study of over 8 million people conducted by Verizon, the number of people who fell for these attacks in 2014 was 11%, increasing to 12% in 2015. While 12% may not sound like a large number, it is important to keep in mind that a major breach into an organization only requires one person to take the bait. So, it is easy to understand why we hear about companies falling victim to cyberattacks on a near weekly basis.
 There are two primary types of attacks: Generic phishing and spear-phishing. Generic phishing attacks are
There are two primary types of attacks: Generic phishing and spear-phishing. Generic phishing attacks are
more common and what most people think of when they hear the term. An email is sent out, often to thousands or even hundreds of thousands of people at one time. The email appears to be sent on behalf of a well-known organization such as PayPal, eBay, or Apple. In other cases, the email may appear to be sent from a bank or credit union, government agency such as the IRS, or even from a service company such as FedEx. No matter from whom the email appears in your In box, the point is that it will often look very legitimate and generally include a link you are asked to click on or an attachment you are requested to open.
In the old days the generic phishing emails were pretty easy to spot due to the vast amount of typos and incorrect use of the English language. However, cyber criminals have evolved and often these phishing emails will now appear very legitimate with the inclusion of company logos, specific details about the organization, and in some cases even your complete name and address. Now, obviously if you don’t have an account with PayPal and you receive an email explaining that for security purposes you need to update your password, it should be pretty easy to detect the email is fake. However, criminals are not targeting any specific person with a generic attack. By sending out thousands of these emails, they know that the odds are good that some people will actually have an account and might just click on the link or open the attachment.
 Spear-phishing is often far more difficult to detect. This is because the cyber criminals will do research ahead of time about the victims they are planning to target. This allows them to send an email that looks like it was sent on behalf of one of your colleagues. In addition, the email will often be crafted to cover a topic that would be logical to send and receive at your place of work. For example, a criminal may use LinkedIn to find out the name of an employee in the HR department at your organization. Then they may send email to the employees on behalf of the HR department using the real name of the HR employee. The message may include an attachment that the employee is instructed to open in order to confirm that his or her personal information is accurate. In other cases, the email may indicate that an employee needs to follow a link to update information. The difference with spear-phishing is that the email can look very real and if you are not diligent in checking over the message, opening the attachment or following the link is a mistake that can easily be made.
Spear-phishing is often far more difficult to detect. This is because the cyber criminals will do research ahead of time about the victims they are planning to target. This allows them to send an email that looks like it was sent on behalf of one of your colleagues. In addition, the email will often be crafted to cover a topic that would be logical to send and receive at your place of work. For example, a criminal may use LinkedIn to find out the name of an employee in the HR department at your organization. Then they may send email to the employees on behalf of the HR department using the real name of the HR employee. The message may include an attachment that the employee is instructed to open in order to confirm that his or her personal information is accurate. In other cases, the email may indicate that an employee needs to follow a link to update information. The difference with spear-phishing is that the email can look very real and if you are not diligent in checking over the message, opening the attachment or following the link is a mistake that can easily be made.
What’s the risk of a link in an email?
What is so bad about clicking on a link? Depending on the goal of the cybercriminal, clicking on a link can lead to numerous security issues. In some cases, the cybercriminal is interested in stealing login credentials or personal information. With those attacks, clicking on the link will take you to a website that looks like the organization the email claimed to be from. So if an email appears to come from PayPal, the website will look like PayPal and may even have a link that appears to belong to PayPal, but is slightly different. For example, it might be www.paypalconfirm.com. The site often will have a webpage that looks like it was setup specifically for the purpose of the email.
For example, if the email tells you that you need to update your security settings, the web page will include the PayPal logo and the page will talk about security. Somewhere on the page will be some form fields that will ask for information such as your login and password. In other cases, it may ask for your credit card information, social security number, home address, drivers license number, etc. The information requested will vary, but the basic concept is always the same; a form that requires you to provide information. When you provide this information, the criminal is able to record everything that of course, will be used against you later.
 In other cases, the criminal’s goal may be to compromise your computer. In those cases, clicking on the link may take you to a malicious website designed to exploit your web browser or other third party applications on your computer such as Adobe Flash. In these situations, the website might appear perfectly normal to you, yet malware is being installed on your computer just because you visited the web page. This is because criminals continue to discover new vulnerabilities in the software running on computers. Serious security vulnerabilities continue to be discovered in Adobe Flash on a monthly basis. These flaws allow cyber criminals to gain control of your computer when you simply visit their web pages. You don’t need to choose to install software, click approve, or even receive a notice that the malicious software is being installed. Keeping up with security patches will help reduce your risk, but often these vulnerabilities are discovered and exploited days, weeks, and even months before a security patch becomes available.
In other cases, the criminal’s goal may be to compromise your computer. In those cases, clicking on the link may take you to a malicious website designed to exploit your web browser or other third party applications on your computer such as Adobe Flash. In these situations, the website might appear perfectly normal to you, yet malware is being installed on your computer just because you visited the web page. This is because criminals continue to discover new vulnerabilities in the software running on computers. Serious security vulnerabilities continue to be discovered in Adobe Flash on a monthly basis. These flaws allow cyber criminals to gain control of your computer when you simply visit their web pages. You don’t need to choose to install software, click approve, or even receive a notice that the malicious software is being installed. Keeping up with security patches will help reduce your risk, but often these vulnerabilities are discovered and exploited days, weeks, and even months before a security patch becomes available.
One last type of attack will again show you a website that looks very legitimate. However, when you attempt to complete whatever function you were directed to do via the email, the website may prompt you to install software. For example, you may receive an email telling you that a secured message is waiting for you. You are asked to click the included link to a website and then follow the instructions to access the email. When you reach the site, you are told you need to install special security software to decrypt the email. While it may look very real, when you download and install the software, you are actually installing malware on your computer giving the cyber-criminal complete access to it.
 The best advice when it comes to links in emails is to simply never click on them. The problem is that it’s often easier said than done. When possible, if you know the site where the email claims to be sent from, manually type in the URL to go to the site rather than clicking on the link. In addition, pay attention to the actual link. In many cases the URL will contain a domain name that is obviously fake. In the event that you do follow a link, make sure once you reach the site, you never install software or provide any confidential information. When in doubt, always err on the side of caution. If you receive an unsolicited or unexpected email from someone you know that includes a link or attachment, pick up the phone and confirm they really sent it or send them a completely new email to their known email address and confirm the email is legitimate. Also, remember to never provide any confidential information on a website unless the webpage is encrypted. This will be obvious by the HTTPS:// at the beginning of the URL.
The best advice when it comes to links in emails is to simply never click on them. The problem is that it’s often easier said than done. When possible, if you know the site where the email claims to be sent from, manually type in the URL to go to the site rather than clicking on the link. In addition, pay attention to the actual link. In many cases the URL will contain a domain name that is obviously fake. In the event that you do follow a link, make sure once you reach the site, you never install software or provide any confidential information. When in doubt, always err on the side of caution. If you receive an unsolicited or unexpected email from someone you know that includes a link or attachment, pick up the phone and confirm they really sent it or send them a completely new email to their known email address and confirm the email is legitimate. Also, remember to never provide any confidential information on a website unless the webpage is encrypted. This will be obvious by the HTTPS:// at the beginning of the URL.
Below is a list of the more common tactics cyber criminals send as links:
- Never trust a URL that starts with a number.
Example: http://192.168.2.5/PayPal/Security/
- Just because an organization’s name is in the URL, doesn’t mean that it’s legitimate.
Example: http://microsoft.security-information.com
- Even if the link starts with https:// it is still important to pay attention to the rest. This is still a domain starting with a number, which should never be trusted.
Example: https://192.168.190.22
- Criminals will often change a character to make the URL look real. In this case the “w” in news was change to the two “v’s” next to each other. At first glance it looks like a “w.”
Example: http://www.nbcnevvs.com
- This URL sometimes confuses people and they assume they are going to foxnews.com. The slash (/) before foxnews.com indicates that foxnews.com is actually the web page and not the domain name being used.
Example: http://0xC0.0xA8.0x8a.0x03/foxnews.com
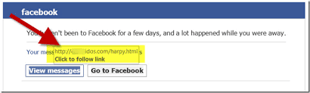 One last thing to remember is that when an email is received, often the page shown to you includes “HTML” somewhere in the name. This is what allows the email to contain colors and pictures. It is important to know that the link address shown to you in the email might not actually be the address you will connect to when you click the link. Move your mouse over the link without clicking it and most mail tools will pop up the real URL where you will be connected.
One last thing to remember is that when an email is received, often the page shown to you includes “HTML” somewhere in the name. This is what allows the email to contain colors and pictures. It is important to know that the link address shown to you in the email might not actually be the address you will connect to when you click the link. Move your mouse over the link without clicking it and most mail tools will pop up the real URL where you will be connected.
Of course, all that said, the best advice is still simply to avoid clicking a link in an email unless you are 100% certain the email is legitimate
What’s the risk of an email attachment?
Most people understand there are risks when opening attachments. That said, thousands of people end up with malware on their computers after opening malicious attachments. It is often a case where the person who became infected was fully aware there are risks with attachments. The problem is that they thought the attachment they were opening was safe. There are a number of reasons for this, but the most common two are (1) that the email came from someone they trusted, or (2) because the type of attachment didn’t seem like something they needed to worry about.
 Let’s start with an email coming from a trusted source. You’re at work and receive an email that appears to have come from the IT department. The email contains a message explaining that a security patch needs to be applied to your computer ASAP. The email is from the IT person and he calls you by name and talks specifically about the patch resolving issues related to a job function that you do. The attachment included is a zip file and for security reasons, the file has been locked with a password that will be sent to you in a different email. It is easy to understand how a person might think this email is legitimate.
Let’s start with an email coming from a trusted source. You’re at work and receive an email that appears to have come from the IT department. The email contains a message explaining that a security patch needs to be applied to your computer ASAP. The email is from the IT person and he calls you by name and talks specifically about the patch resolving issues related to a job function that you do. The attachment included is a zip file and for security reasons, the file has been locked with a password that will be sent to you in a different email. It is easy to understand how a person might think this email is legitimate.
A minute later, a second email arrives from the IT person and this one contains the password and a note asking you to get started ASAP. At this point, you open the zip file, provide the password, and run the patch installation just as you were asked. A minute or two later you are all done and the patch is applied. So you think.
 Of course you didn’t actually install a patch and the email didn’t come from the IT person. This is a very common type of phishing attack where a user is tricked into installing malicious software via an attachment. The reason for the success is that the source of the email appears to be trusted and the message seems very realistic.
Of course you didn’t actually install a patch and the email didn’t come from the IT person. This is a very common type of phishing attack where a user is tricked into installing malicious software via an attachment. The reason for the success is that the source of the email appears to be trusted and the message seems very realistic.
While the message and type of attachment may vary, the goal is always the same; to trick the user into opening the attachment and installing malware. While the example above would require the user to follow a few steps, in other cases you may never even know that something was installed. This leads to malicious attachments that may be sent from trusted or random individuals.
Now, it seems like if you received a malicious attachment from some random person, you would obviously not open it. Yet there is a very good chance in just the past seven days you may have done just that. You see, people have an idea in their mind that a malicious attachment is a very specific type of file, such as an executable or zip file. In reality, numerous other types of attachments can be just as dangerous if not more so. For example, have you ever received a PDF file from a vendor doing business with you? It turns out that Adobe Acrobat, the software most commonly used to view PDF files also has been found to contain numerous security vulnerabilities. That means that if you are not up to date with the latest security patches for Adobe Acrobat, simply opening the PDF file to view it can cause malware to be installed on your computer. Of course you won’t have any idea this has happened because the PDF file will open as normal for you.
 Word docs, spreadsheets, PDF files, and numerous other attachment types can all contain malicious software and be used to exploit vulnerabilities and compromise your computer. Much like links in email, users should be extremely cautious when opening any attachment received in an email. Of course there will be situations where you need to open an attachment sent from a co-worker, but the idea is that the email should be expected when you do. If you receive an unsolicited email from a trusted or non-trusted source, this is the time you should be cautious about opening the attachment. When in doubt, hold off on opening it. If possible, pick up the phone and call the sender of the email or contact someone in IT who can assist you and confirm that the attachment is safe to open.
Word docs, spreadsheets, PDF files, and numerous other attachment types can all contain malicious software and be used to exploit vulnerabilities and compromise your computer. Much like links in email, users should be extremely cautious when opening any attachment received in an email. Of course there will be situations where you need to open an attachment sent from a co-worker, but the idea is that the email should be expected when you do. If you receive an unsolicited email from a trusted or non-trusted source, this is the time you should be cautious about opening the attachment. When in doubt, hold off on opening it. If possible, pick up the phone and call the sender of the email or contact someone in IT who can assist you and confirm that the attachment is safe to open.
Blog provided by Stickley on Security